Cybersecurity- 8 Best Practices When Working From Home
With the holiday season approaching it’s more important than ever to stay on top of cybersecurity. Cybersecurity continues to be a hot topic for everyone, at all levels of an organization.
Awareness & Education
All companies, no matter their size or industry, are threatened by cyber criminals. Educate yourself and your staff on the cybersecurity landscape by incorporating cybersecurity education into your training sessions. Here are 8 best practices remote workers should follow to minimize their cybersecurity risks.
#1 Home Routers
Ensure home routers meet the minimum standards that your employer advises and keep your router updated with the latest firmware. Residential ISP-provided modems and routers offer little in terms of security so be sure to check your company’s recommended router policies. Installing a firewall will provide additional security layers and protections.
#2 Work Computers
Work computers must be installed with company-recommended antivirus software and email security client. Equally as important, install new Windows, iOS, and Android updates and shut down your computers and tablets when not in use. Threats are diminished when your computer is turned off. Alternatively, be sure to lock your computer when not in use.
#3 VPN
Use a Virtual Private Network (VPN) to ensure network traffic is encrypted when accessing critical business applications.
#4 Use REALLY Strong Passwords
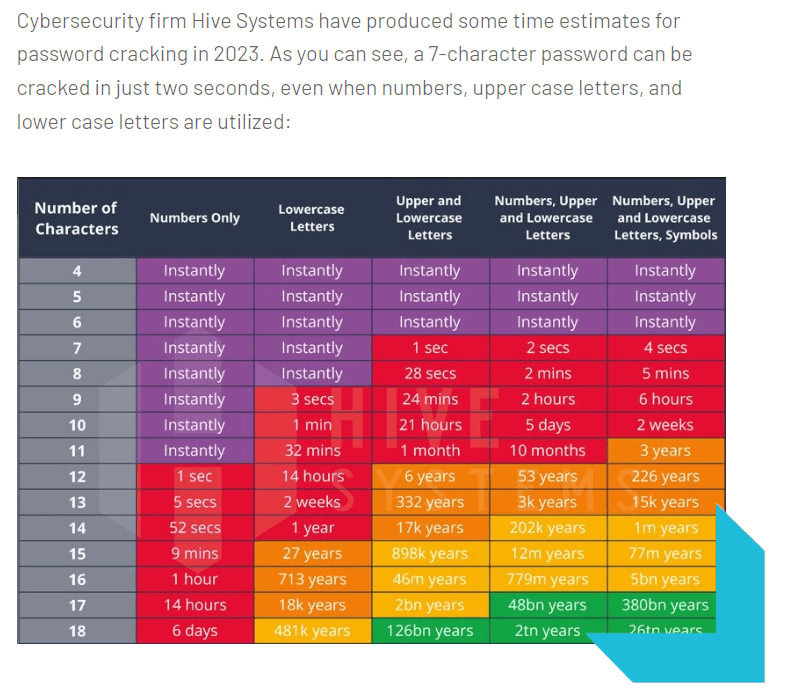
Many experts admit that passwords are not a secure form of security protection since they are so easily hacked, and with the generation of AI, will become even more hackable as bots continue to get ‘smarter,’ by analyzing patterns, and running through millions, if not billions or trillions of password combinations every day. Currently, the recommended password length is 15+ characters, including letters (mix of lowercase and uppercase), numbers, and symbols. It is also recommended to change your passwords every 90 days.
Did You Know?
A 10-character password with a mix of upper/lowercase letters, numbers and symbols can be cracked in less than 2 weeks.
Use a Password Manager
Password Managers provide long, varied, unique passwords for all of your accounts without having to remember them. According to Tech.co, the best Password Managers “deploy zero-trust security architecture that make it near-impossible to obtain passwords stored in their vaults, even if a hacker breaches their systems.”
Never Use the Same Password Across Multiple Accounts
Once a hacker has guessed your password for one site, they can crack other sites using a technique calling ‘credential stuffing.’ Credential stuffing refers to using the same username and password combinations on a variety of other sites including Facebook, X, Gmail, etc. It is crucial to never use the same password across multiple accounts. Likewise, you should never share your passwords with others.
#5 Security Layers
Implementing multifactor or two-factor authentication (MFA/2FA), or Google Authenticator, can provide additional layers of security to safeguard your accounts.
#6 'Email is a Battleground' Mindset
Love it or hate it, email is still one of the most popular forms of communication for businesses. Unfortunately, it’s also one of most popular ways hackers obtain sensitive information through ‘phishing’ attempts (aka it’s a lot easier if you unknowingly give your credentials to hackers versus having to crack them). Keeping the mindset that ‘email is battleground’ means you are constantly on the lookout, taking a persistent approach to defending your inbox, which in turn heightens your awareness- making it easier to spot the bad actors.
Tips to Spotting a Phishing Email:
Always look at the ‘from’ email address. For example, the email may state it’s from “Apple” but if the email address’ domain is not from ‘@apple.com,’ it’s not from Apple. Other tips include:
- Check for spelling/grammar mistakes
- Urgency – a time-sensitive request to take action
- Pressuring the email recipient to click a link or open an attachment.
#7 Use Secure Cloud Applications with Backup & Restore Capabilities
Use secure cloud applications to access work documents and transfer data, and implement a secure backup software solution for critical documents and applications.
#8 Report Suspicious Activities Immediately
Encourage your employees to immediately report any suspicious activities to the IT department or leadership.
Established in 1979, ACC Telecom is a B2B telecommunications company that specializes in remotely working solutions such as teleworking and business communications systems. Contact ACC Telecom today to learn more about office and remote working solutions.

